Several hundred staff have lost internal network access -sourceBank memo alerts global workforce to cyber attack threatUnclear when access might...
Computer Network
Digital marketing is a great way to speed up your business growth. Every year, unexpected digital trends arise to provide...
It's easy to find your Wi-FI passwords on Mac OS and windows. Ian Hooten/Science Photo LIbrary/Getty Images When you log...
A certification has the role of attesting to the competence of a person in a particular field. Thus, by obtaining...
CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how...
From a new iPhone SE and iPad Air to a beefy M1 Ultra chipset, Apple's spring hardware event brought refreshed...
1. Reconnaissance First in the ethical hacking methodology steps is reconnaissance, also known as the footprint or information gathering phase....
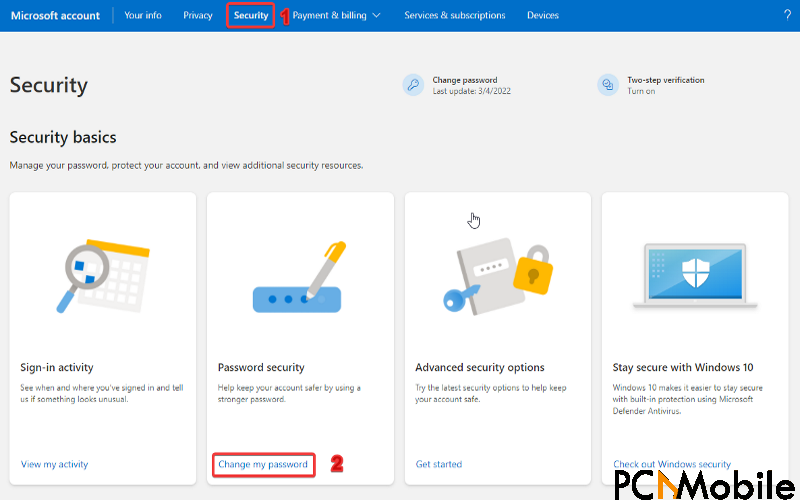
Are you trying to change your Microsoft Outlook password but can’t do so? Well, you are at the right spot....
A government computer system got bogged down during Saturday's deadly central Iowa tornado outbreak, slowing down the flow of meteorologists'...






/cloudfront-us-east-2.images.arcpublishing.com/reuters/RXZZTOWDDFJSPASCIDKCBQ462U.jpg)