Welcome to Cyber Security Today. This is the Week in Review edition for Friday, March 11th, 2022. I’m Howard Solomon,...
Nyc College Of Technology
Digital marketing is a great way to speed up your business growth. Every year, unexpected digital trends arise to provide...
A certification has the role of attesting to the competence of a person in a particular field. Thus, by obtaining...
CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how...
From a new iPhone SE and iPad Air to a beefy M1 Ultra chipset, Apple's spring hardware event brought refreshed...
1. Reconnaissance First in the ethical hacking methodology steps is reconnaissance, also known as the footprint or information gathering phase....
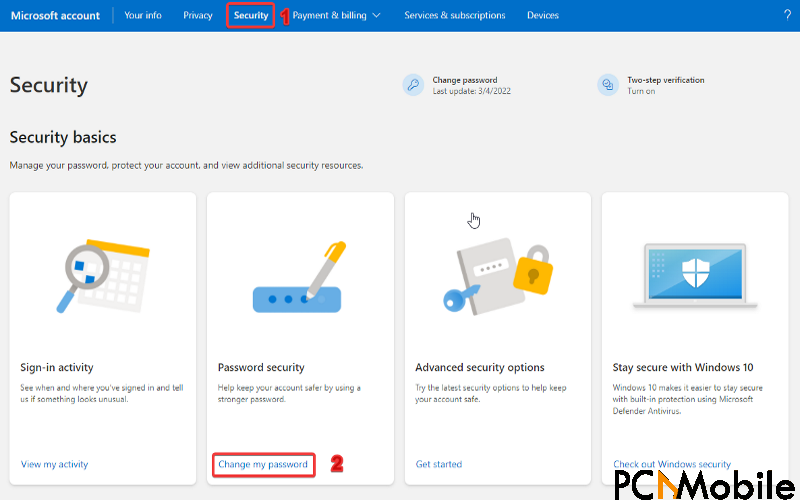
Are you trying to change your Microsoft Outlook password but can’t do so? Well, you are at the right spot....